Digital signatures are a key component of secure business processes. Contracts are signed digitally, documents are sent electronically, and approvals can be granted from anywhere. At the same time, the question arises: Just how secure is this, really?
When used correctly, digital signatures provide a reliable foundation for digital workflows. They ensure that a document’s origin remains traceable and that its content cannot be altered without being detected. As a result, they go beyond a simple digital signature and become a key component of IT security and legally compliant processes.
How does a digital signature work?
Digital signatures work based on a clearly defined cryptographic process. The goal is to ensure two things: the identity of the signer and the integrity of the document.
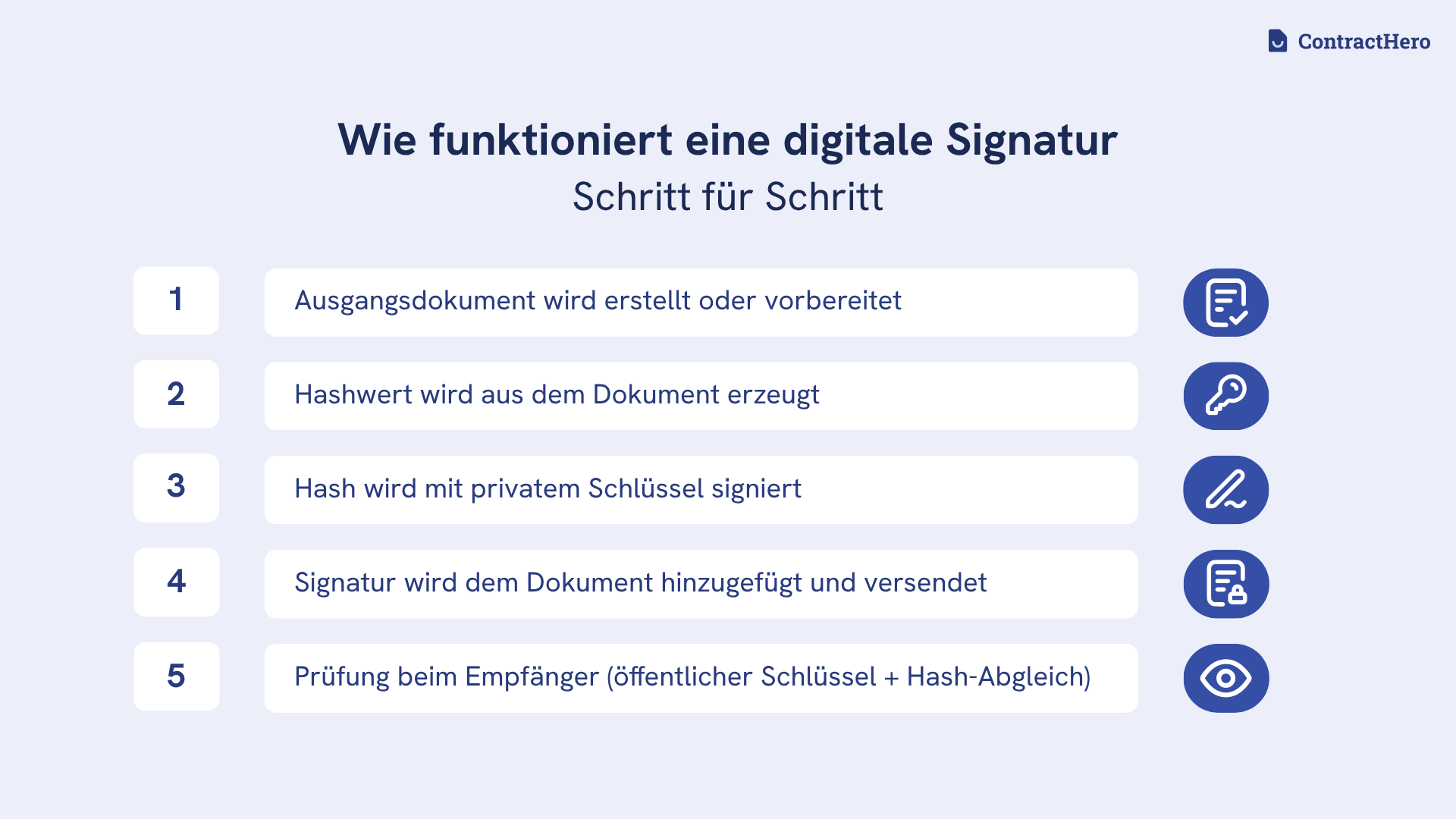
The first step involves generating a so-called hash value from the document to be signed. This hash is a unique, irreversible checksum of the content. Even the slightest changes to the document result in a different hash value.
This hash value is then encrypted using the signer's private key. The result is the digital signature, which is attached to the document. The private key remains exclusively in the signer's possession and must not be disclosed to anyone else.
During verification, the process runs in reverse. The recipient decrypts the signature using the signer’s public key, thereby obtaining the original hash value. At the same time, the recipient calculates a new hash from the received document.
If both values match, it is clear that the document was created by the specified signer and is in its original state. If the values do not match, the signature is invalid.
It is precisely this mechanism that makes digital signatures secure. Any tampering becomes visible and cannot be carried out without being noticed.
Security of Digital Signatures
The security of digital signatures is based on three key properties: authenticity, integrity, and non-repudiation.

Authenticity ensures that a digital signature can be uniquely linked to a person or organization. This is based on cryptographic keys combined with a digital certificate that verifies the identity.
At the same time, integrity ensures that a document cannot be altered without being detected after it has been signed. Even the slightest changes become visible and invalidate the digital signature.
In addition, the binding nature of the digital signature ensures that it can be legally attributed to the signatory. This creates a robust and traceable foundation for legally compliant digital business processes.
Compared to traditional signatures, digital signatures offer a higher level of security. The difference lies in verifiability. Handwritten signatures can only be assessed visually, whereas digital signatures rely on cryptographic methods.
This requires proper implementation using trusted digital certificates and correctly integrated signature processes. Only then can the digital signature become a central component of modern IT security and reliable document security.
Can digital signatures be forged?
Whether a digital signature can be forged depends less on the method itself than on how it is implemented in practice. The cryptographic methods used are well-established and widely employed.
Vulnerabilities typically arise outside the scope of the digital signature. These include inadequate identity verification, insecure access processes, or poorly secured end devices. In such cases, it is not the digital signature itself that is tampered with, but rather the underlying signing process that is exploited.
Clear safety standards are essential during implementation. These include:
- Identity verification prior to the issuance of a digital certificate
- Use of qualified trust service providers under eIDAS
- Secure storage of keys, e.g., in hardware modules
- Access protection through multi-factor authentication
- Regular review and revocation of compromised certificates
If digital certificates and signature processes are implemented properly, the risk of undetected forgery can be virtually eliminated.
Electronic Signature vs. Digital Signature
The terms "electronic signature" and "digital signature" are often used interchangeably. However, they are distinct concepts, each with its own specific meaning.
An electronic signature is a general legal term. It encompasses all forms of signatures created electronically, regardless of the technical method used. This includes simple click-based approvals, scanned signatures, and more complex signature procedures.
A digital signature, on the other hand, refers to a specific technical process. It is based on cryptographic methods and ensures that a document has not been altered and can be uniquely attributed to a specific person.
The key distinction is this: Every digital signature is an electronic signature, but not every electronic signature meets the technical and security requirements of a digital signature.
This distinction is relevant in a business context. While simple electronic signatures can be implemented quickly, digital signatures provide a higher level of technical security and traceability.
Differences and similarities
The difference is most evident in the weight of the evidence and the context in which it is used.
Electronic signatures are versatile and can be used in many everyday situations, such as internal approvals or simple agreements. However, their legal enforceability depends on the specific procedure and documentation involved.
They can be verified independently of the original system. They enable standardized signature verification that works independently of the original system. This makes them particularly relevant in regulated or high-risk processes.
Another difference lies in the effort involved. Electronic signatures can be used without any technical hurdles. Digital signatures require an infrastructure consisting of certificates, identity verification, and clearly defined processes.
What both approaches have in common is that they replace paper-based workflows and streamline digital processes. Documents can be signed from anywhere and processed further without any disruption in the workflow. At the same time, consent is digitally documented and recorded in a traceable manner.
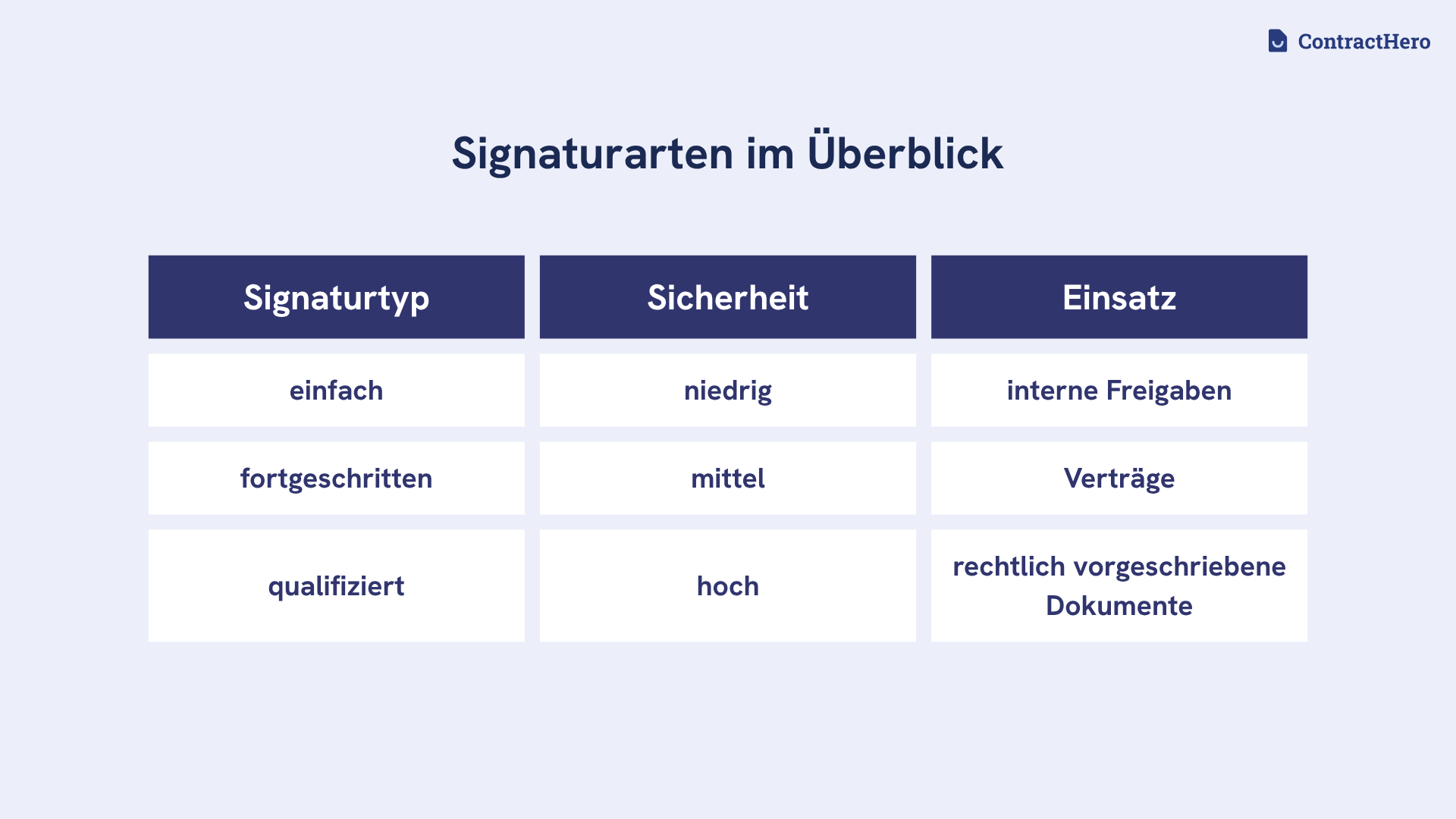
Legal validity in the EU
In the EU, the validity of digital signatures is governed by the eIDAS Regulation. It establishes uniform standards for electronic signatures and distinguishes between three levels: simple, advanced, and qualified electronic signatures.
As a general rule, a digital signature is legally valid unless prohibited by a statutory form requirement. For many everyday uses, a simple electronic signature is sufficient.
The advanced electronic signature goes one step further. It is uniquely linked to the signatory and enables the signatory to be identified. At the same time, it is linked to the document in such a way that any subsequent changes can be detected.
However, whenever written form is required, a qualified electronic signature is necessary. This is based on a verified digital certificate and is created through certified trust service providers. Legally, it is equivalent to a handwritten signature.
For businesses, classification is crucial. Choosing the appropriate signature level determines whether documents are legally valid in the event of a dispute and will hold up in court.
Examples of use
Digital signatures are used in many business processes, particularly where traceability and security are required. Typical examples of digital signatures include contract management, the signing of proposals, NDAs, and employment-related documents.
Digital signatures also play an important role in the financial sector. Contracts in online banking, loan agreements, and compliance-related approvals are increasingly being digitally signed to speed up processes while ensuring that they are documented in an audit-proof manner.
Another area of application is communication with government agencies, such as when filing tax returns or responding to public tenders. In these cases, a higher level of digital signature is often required to meet legal requirements.
The choice of the appropriate solution depends on the level of risk and the legal classification. The more sensitive a document is, the more important it is to use secure and traceable signature procedures.
What is a digital certificate?
A digital certificate is the basis for ensuring that a digital signature can be uniquely linked to a person or organization. It functions like a digital ID and confirms that a specific public key belongs to a verified identity.
Digital certificates are issued by so-called trust service providers, whose requirements and verification processes are regulated at the European level by the eIDAS Regulation. The EU’s Trusted List provides an overview of approved providers. These providers verify the identity in advance and link it to a cryptographic key pair. The certificate itself contains, among other things, information about the identity, the issuer, and the validity period.
This association is crucial for digital signatures. Only when it is clear who owns a key can a signature be reliably verified and traced.
In a business context, the appropriate certificate level is crucial. Depending on the requirements, different certificates are used, such as those for advanced or qualified electronic signatures.
Digital certificates thus form the technical foundation for secure and traceable signature processes.
Encryption and digital signatures – how are they related?
Digital signatures and encryption are based on similar cryptographic methods, but serve different purposes.
A digital signature ensures that a document's origin can be traced and that its integrity is preserved. Encryption is applied to the content itself and ensures that only authorized recipients can access the information.
The two processes are interrelated but serve distinct purposes. The digital signature verifies a document’s origin and integrity, while encryption protects its confidentiality.
In practice, both mechanisms are used together. Documents are signed to ensure traceability and then encrypted to control access.
Digital signatures and encryption thus complement each other as key components of secure and controllable digital processes.
Document security through digital signatures
Digital signatures enhance document security by reducing common vulnerabilities in digital processes. These include unnoticed changes, missing evidence, and unclear responsibilities.
The signature ensures that a document is technically secure and that its integrity can be verified at any time. If the content is altered, the signature becomes invalid.
At the same time, this ensures clear traceability. The time of signing, the signatory, and the verification status are recorded by the system and can be viewed at any time. This creates transparency and reduces uncertainty, particularly in audit-related or sensitive processes.
Digital signatures ensure that documents are structured, verifiable, and audit-proof, thereby enhancing document security in day-to-day operations.
Signature Verification in Practice
Signature verification ensures that a digital signature is valid and that a document remains in its original state. It ensures that signed documents can be used and processed reliably.
In practice, the signature verification process is largely automated. Systems check whether the digital signature is technically valid, whether the digital certificate is valid, and whether it was issued by a trusted provider. They also verify whether the certificate was active at the time of signing or had already been revoked.
Another key step is the integrity check. This verifies whether the document has been altered since it was signed. If so, the signature is deemed invalid.
This process is critical for businesses. Only verified digital signatures provide a solid foundation for contracts, approvals, and compliance-related processes.
Modern software solutions integrate signature verification directly into existing workflows. This allows the process to run in the background while ensuring the reliability of the documents.
Conclusion
Digital signatures are a key component of modern IT security. They ensure the traceability of digital processes and protect documents from unauthorized alterations.
The decisive factor is not the technology alone, but how it is implemented. A robust level of security can only be achieved through verified digital certificates, clear processes, and the appropriate level of digital signature. This is precisely where simple digitization differs from controlled, legally compliant processes.
For businesses, this is about more than just efficiency. Digital signatures provide a reliable foundation for document security, compliance, and transparent decision-making. They mitigate risks in areas where traditional processes fall short.
Organizations that implement structured signature processes gain control over documents, responsibilities, and records, thereby laying the foundation for secure and scalable digital business processes.


.avif)
.svg)











.jpg)