What is ISO 27001?
ISO/IEC 27001 is an internationally recognized standard for information security. It describes how companies can systematically protect their sensitive information. This includes, for example, customer data, contract documents, access rights, and internal processes. At the core of the standard is an information security management system (ISMS): a clearly defined procedure for identifying risks, implementing appropriate protective measures, and reviewing them regularly.
The requirements are particularly high in Germany: the Federal Data Protection Act (BDSG) and the GDPR specify how personal data may be processed (fairly and lawfully, only for clear purposes, correctly, and up to date). For many companies, practical implementation is a challenge. ISO 27001 provides a proven framework for organizing data protection and information security in a structured manner.
Important: ISO 27001 certification does not just mean "we pay attention to security," but that the ISMS has been audited by an independent body. This allows a company to demonstrate that information security and compliance are not left to chance, but are firmly anchored in everyday life.
What does ISO 27001 certification cost?
The costs of ISO 27001 certification can vary greatly depending on the size of the company and the complexity of its existing structures. The certification process consists of several phases, each of which incurs costs. The costs listed below are therefore indicative values:
- Implementation phase: The costs depend on the measures required to establish a suitable information security management system (ISMS).
- Certification costs: For smaller companies, the expenses amount to approximately €6,000 to €14,000, while larger companies can expect to pay €15,000 to €35,000.
- Surveillance audits: In subsequent years, costs of approximately €4,000 to €8,000 per year will be incurred to ensure compliance with the standard.
- Internal audits: These cost around €3,000 to €5,000 per audit. Such internal audits should be carried out annually before the external audit.
- Additional tools: Software solutions or security measures such as password protection can cost between €1,000 and €2,000.
The certification is valid for three years. The certification itself is carried out in the first year, followed by surveillance audits in the second and third years. Recertification after the three years have expired then incurs further costs. Overall, a company should therefore factor in not only the one-off costs, but also the follow-up costs.
Who is authorized to issue ISO 27001 certificates?
ISO 27001 certificates may only be issued by independent, external certification bodies. These bodies conduct an audit to check whether the company meets the requirements of the standard and issue the certificate if the audit is successful.
Important: The certification body itself must be accredited. This accreditation is proof that it works in a professionally competent, independent, and credible manner and ensures that the certificate is recognized by customers and authorities. In Germany, the DAkkS (German Accreditation Body) is particularly relevant in this regard.
Objectives and benefits of ISO 27001 certification
Many companies know that ISO 27001 makes sense, but still postpone certification. Yet it is often a clear lever for greater security, less risk, and more trust, and is therefore frequently required in practice.
The most important goals and benefits at a glance:
- Better protection of information, data, and business processes
They establish clear rules, responsibilities, and protective measures for sensitive information. - Fewer business and liability risks
Risks are systematically identified, assessed, and reduced before anything happens. - Greater trust among customers and business partners
An externally audited ISMS is verifiable proof of reliable security standards. - Stronger and more stable IT and security processes
Processes are documented, reviewed, and continuously improved.
ISO 27001 helps to identify gaps in information handling and close them in a structured manner.- Greater security awareness within the team
Employees receive training and are made aware of data protection and information security from the outset. - Save costs by reducing security incidents
Prevention is usually significantly cheaper than the consequences of an incident (e.g., downtime, damage, effort).
Which companies need ISO 27001?
ISO 27001 is particularly important for companies that operate critical infrastructure (KRITIS)—i.e., organizations whose failure would have serious consequences for the community. These include areas such as energy, health, transportation/traffic, finance, telecommunications, and other central utility services.
For KRITIS operators, proof of adequate IT security in accordance with Section 8a BSIG is also relevant. An ISO/IEC 27001 certificate can be used as part of this proof, provided that the framework conditions specified by the BSI are met.
But even outside of KRITIS, information security is a management issue: management teams must adequately manage risks such as IT and cyber risks and avoid damage or legal violations. Although ISO 27001 certification is not always required by law, it is often used as a recognized, verifiable standard to demonstrate security levels and due diligence.
ISO 27001 requirements at a glance
The certification serves as an important indicator that a company organizes and manages its information security practices according to internationally recognized standards. With an ISO 27001-certified organization, it can be assumed that:
1. A robust information security management system (ISMS) is in place and continuously reviewed for effectiveness. This system includes policies, processes, and procedures designed to protect all information, from customer data to trade secrets.
2. Regular risk analyses are conducted to identify and close security gaps. The organization has developed mechanisms to systematically assess risks and take appropriate measures to address current and future threats at an early stage.
3. Promote a strong awareness of security and provide appropriate training for all employees, ensuring that staff understand the importance of information security and implement it in their daily work.
4. Security measures are implemented at all organizational levels, including technical, organizational, and physical measures that demonstrate a comprehensive commitment to protecting sensitive data and systems.
5. Compliance with external regulations and legal requirements is ensured, which is of great importance in regulated industries. Certification helps organizations to effectively meet compliance requirements such as the GDPR.
How does ISO 27001 certification work?
The certification process can be divided into three phases. The duration depends on the size of the company and the measures already implemented. Small companies can achieve certification within six months, while large companies may need more than a year. Therefore, the values mentioned are only guidelines:
Preparation and analysis of the current situation
The first question is: What exactly needs to be certified? To answer this, you need to define the scope of your ISMS—i.e., which locations, teams, systems, and processes are included. This scope will be reviewed later in the audit and must be clearly defined.
This is followed by a gap and risk analysis: you check which requirements you already meet and where there are still gaps. This results in a realistic project plan with roles, schedule, and priorities.
Typical steps:
- Define scope: Which areas, locations, IT systems, and processes are part of the ISMS? (This scope will be reviewed later in the audit.)
- Gap analysis & risk analysis: What requirements are already met, where is action needed, and which threats are most critical?
- Plan and implement measures: Define and introduce guidelines, responsibilities, and controls (e.g., access concepts, password rules, incident processes).
- Collect documentation and evidence: Record everything in a way that can be verified (e.g., guidelines, protocols, tickets, training certificates).
Internal audits and documentation
Now the ISMS becomes "tangible": guidelines, processes, and controls are documented and implemented in everyday life. A good comparison is a security manual that shows how your company handles information, from access rights to emergency plans.
Important components include:
- Security policy and roles and responsibilities
- Risk assessment and risk treatment plan (how you deal with risks)
- Statement of Applicability (SoA) (which measures apply – and why)
training and emergency plans Evidence that the measures are actually being implemented (e.g., logs, tickets, reports)
Before it goes public, there is a dress rehearsal:
- Internal audit: You check whether processes and controls are actually being implemented and document any deviations.
- Corrective measures: Any vulnerabilities found are fixed and tracked in a way that's easy to follow.
- Management review: Management evaluates the status of the ISMS and decides what needs to be improved.
This is followed by the external audit in two stages:
- Stage 1: Documentation check (is everything described completely and coherently?)
- Stage 2: Implementation check (interviews, process observation, spot checks – is the ISMS evident in everyday work?)
If both stages are successful, the certificate will be issued.
How long does the certification process take?
The duration depends heavily on how well your structures are already in place. Many companies need several months, and even longer for complex structures. However, companies with existing security processes or an already established ISMS are usually much faster.
As a rough guide:
- Preparation & setup: often several months (depending on maturity)
- Certification audit: Stage 1 + Stage 2 follow depending on project status
- Validity: The certificate is valid for 3 years.
- Surveillance audits: Usually annually during the term
- Recertification: after 3 years – usually sooner, because much of the work has already been done
It is important to note that ISO 27001 is not a "one-time" task, but rather a system that is continuously improved (plan, implement, review, improve).
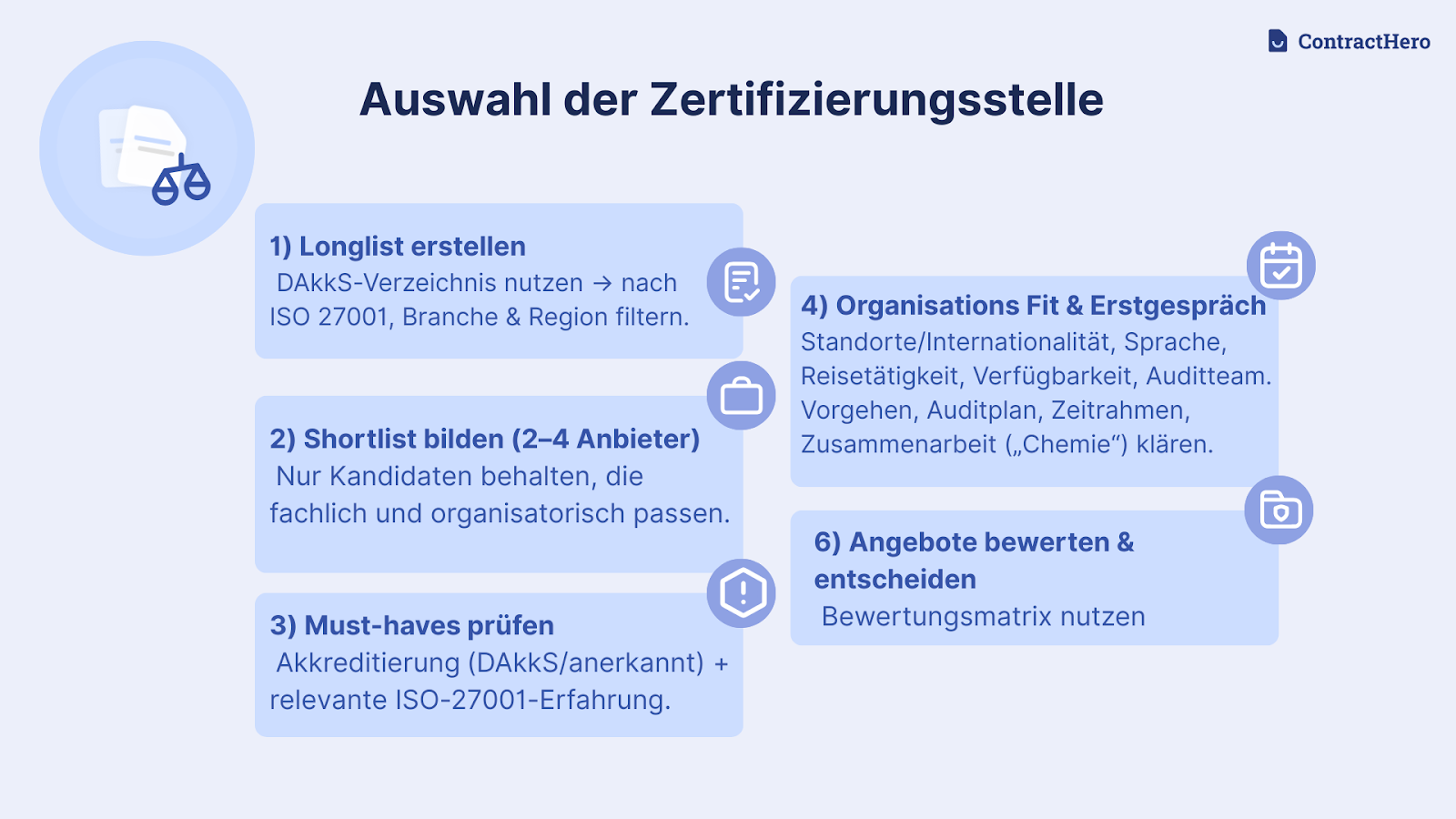
Selection of the certification body
Choosing the right ISO 27001 certification body is a key step in the certification process. This is because it not only affects costs and scheduling, but also how pragmatic and smooth the audit process is. The following overview shows the most important steps.
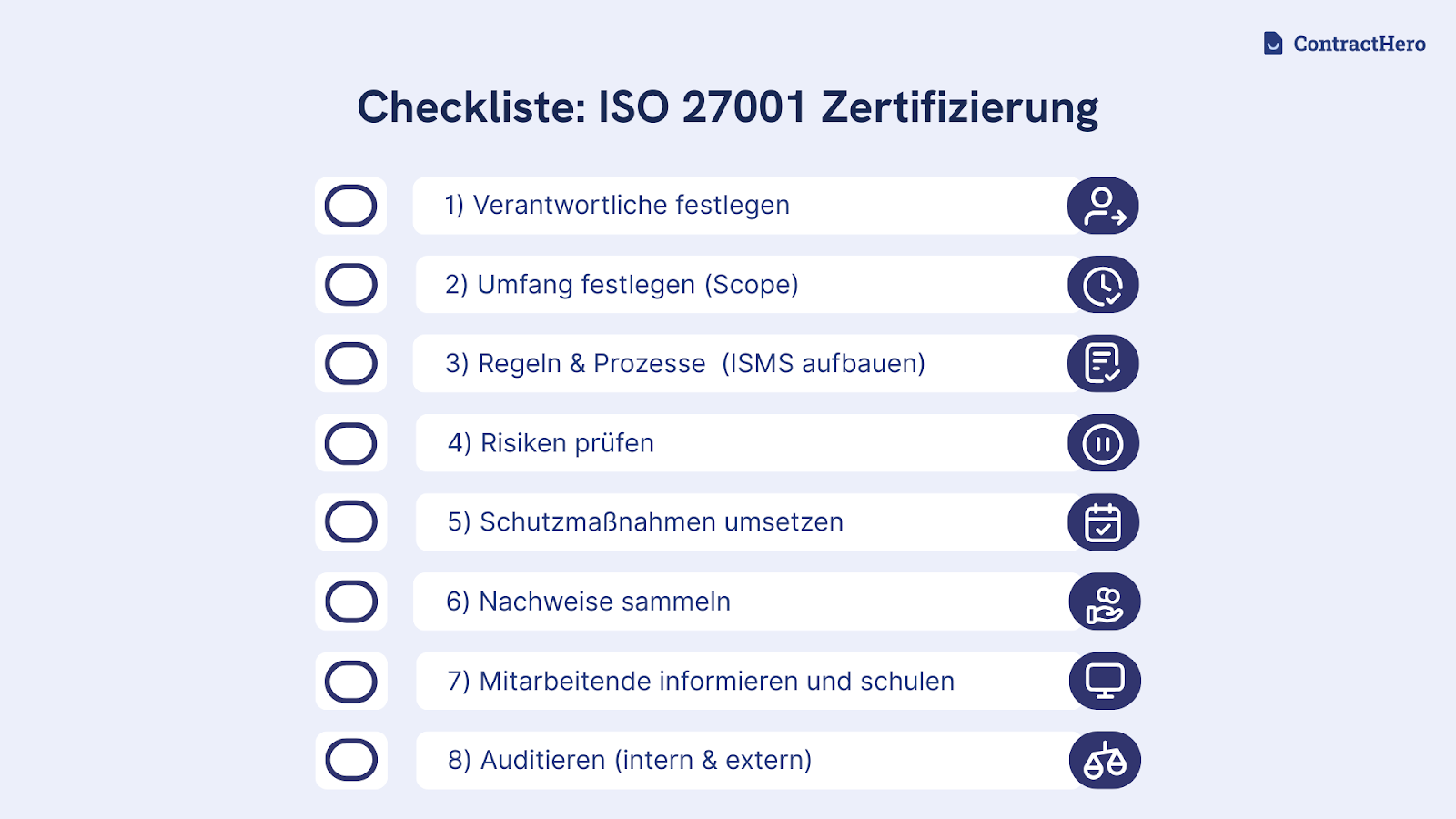
Checklist for ISO 27001 certification (explained simply)
At first glance, ISO 27001 certification seems complex, but it can be easily planned if the process is broken down into clear steps. The following checklist shows the most important tasks, from ISMS planning to risk analysis and audits to ongoing improvement after certification.
1) Appoint responsible persons
Appoint a small team and define clear responsibilities. Without ownership, ISO 27001 quickly becomes a side project.
- Appoint an ISO 27001 team
- Define roles and responsibilities
- Involve management early on
2) Define scope
Define which areas, systems, and locations are to be "certified." This framework must be clearly documented.
- Define scope (areas, locations, systems, processes)
- Communicate and document internally within Scope
3) Write down rules and processes (set up ISMS)
Create the most important security rules and procedures: Who has access to what? What happens in the event of a security incident?
- Set up ISMS framework (plan, implement, review, improve)
- Create and publish policies, processes, and documentation
- Adapt templates to the organization (language, processes, responsibilities)
4) Assess risks
Take a structured approach: What could happen, how likely is it, and what would be the impact? This will help you set priorities.
- Define risk management approach
- Identify risks, assess probability of occurrence and impact
- Prioritize risks
- Define action plan for each risk (treat, avoid, accept, transfer)
5) Implement protective measures
Implement measures that actually reduce the most significant risks (not just "paper security").
- Review the catalog of measures from ISO 27001 (Annex A) and select the controls that demonstrably reduce your greatest risks.
- Implement measures and ensure effectiveness in everyday life
6) Collect evidence
ISO 27001 thrives on traceability: you must be able to demonstrate that rules exist and are being implemented.
- Collect documents, logs, protocols, tickets, and training certificates
- Maintain list of required documents/records for the audit
- Continuously monitor the effectiveness of controls
7) Inform and train employees
Everyone should know the basics, especially regarding data, access, and incidents.
- Create a communication plan (who needs to know what?)
- Distribute guidelines and document acknowledgment in a traceable manner
- Conduct training (regularly, role-based, practical)
8) Internal testing (internal audit)
Conduct a dress rehearsal: Where are there still issues before the certification body arrives?
- Define internal audit methodology and scope
- Employ independent internal auditors
- Document and close findings (follow up on corrective measures)
9) External audit – Part 1 (Stage 1)
This mainly concerns your documentation: Is everything described completely and coherently?
- Appoint an accredited certification body
- Have documentation checked
- Gather feedback and establish audit readiness
10) External audit – Part 2 (Stage 2)
Practical application is what counts here: Is the ISMS really being implemented in everyday life?
- Demonstrate implementation in everyday life (interviews, spot checks, process observation)
- Correct and document nonconformities
- Receive certificate
11) Keep at it
The certificate is valid for three years and is reviewed regularly. Keep your ISMS up to date and improve it continuously.
- Conduct management reviews regularly (e.g., annually/quarterly)
- Repeat annual risk analyses
- Prepare surveillance audits (years 1 and 2)
- Plan recertification after 3 years
- Implement and document continuous improvements (including nonconformities until "closed")
The ISO 27001 security concept
ISO 27001 is so widespread because the standard works for almost every organization. It covers the entire information security management system (ISMS) and takes into account not only technical but also organizational processes and evidence. The focus is on the question of what risks exist for information and how to control them. Appropriate measures are then derived from this. ISO 27001 is also certifiable: an independent body audits the system and officially certifies it. Many alternatives, on the other hand, are more narrowly tailored or pursue a different goal, such as a minimum technical standard or a report as proof for customers.
Specifically, this "concept" typically includes:
- Who is responsible for what (e.g., IT, security, specialist departments, management)?
- What are the risks to information (e.g., data loss, unauthorized access) and how are they handled?
- Practical measures such as access controls, MFA (multi-factor authentication), backups, contingency plans, supplier verification, and logging.
- Rules and processes are documented and verifiable.
- Employees know how to behave safely and what to do in an emergency.
- Internal audits, management reviews, and continuous improvement (not "do it once and you're done").
In short, the security concept according to ISO 27001 is the structured approach that a company uses to make information security plannable, measurable, and permanent.
Differences: ISO 27001 vs. other standards
ISO 27001 is primarily a management standard. It describes how a company can organize information security on a permanent basis. Many other standards focus on different areas: some are industry- or country-specific, some are more like test reports for customers, and others are legal requirements.
ISO 27001 vs. GDPR
The GDPR is a legal requirement in the EU. It regulates the protection and confidentiality of personal data and stipulates how it may be processed. ISO 27001 is not a law, but a management standard. It helps to implement information security in a structured manner and thus supports GDPR compliance, but does not replace it.
ISO 27001 vs. SOC 2
SOC 2 is often an audit report that shows customers whether certain controls are effective, for example, in terms of security, availability, or data protection. ISO 27001 takes a more comprehensive approach to the issue: it requires a permanently functioning management system that manages risks and continuously improves. SOC 2 is more of a proof of control, while ISO 27001 is more the system behind it.
ISO 27001 vs. TISAX®
TISAX® is specifically designed for the requirements of the automotive industry and its supply chains. ISO 27001 can be used across all industries and worldwide. A TISAX® label is not automatically the same as ISO 27001 certification—the standards have different objectives and assessment logics.
ISO 27001 vs. Cyber Essentials
Cyber Essentials is a UK scheme with a few clearly defined minimum technical measures against common online threats. ISO 27001 is much more comprehensive: in addition to technology, it also covers organization, processes, risk analysis, and continuous improvement. Cyber Essentials is more of a baseline check, while ISO 27001 is a complete security management system.
ISO 27001 vs. NIST CSF
The NIST Cybersecurity Framework is a guidance framework. It structures cybersecurity work into functions such as Identify, Protect, Detect, Respond, and Recover. ISO 27001 is structured more specifically as a management system and provides a certifiable basis. NIST CSF helps with structure and maturity, while ISO 27001 provides the auditable evidence framework.
Comparison with BSI basic protection
BSI IT-Grundschutz and ISO 27001 pursue the same goal (information security), but the approach is often different: Grundschutz works more with predefined building blocks and measures, while ISO 27001 typically uses a risk-based approach.
- In IT baseline protection, organizations first implement basic/standard protection in accordance with BSI methodology; only then is it determined where additional measures are necessary.
- As a result, IT baseline protection is often more formalized and may require more documentation and coordination during implementation. However, the process is clearly structured in stages and standardized.
ISO 27001 vs. ISO 27701
ISO 27001 regulates information security as a whole. ISO 27701 supplements (or expands) this approach to include data protection, i.e., the structured handling of personally identifiable information (PII) in processes, roles, and documents.
- ISO 27701 establishes a Privacy Information Management System (PIMS) that systematically translates privacy requirements into the organization.
- The focus is more on questions such as: What personal data do we process? For what purpose? Who is responsible (controller/processor)? How is the life cycle (from collection to deletion) managed?
- In short: ISO 27001 = "General information security," ISO 27701 = "Security + clear data protection structure for personal data."
Particularly in contract management, where highly sensitive data is processed, ISO 27001 creates a reliable basis for cooperation and trust. For many companies, choosing an ISO 27001-certified provider can reduce the effort involved in security and compliance audits because essential requirements and evidence are available in a structured form. ContractHero is ISO 27001 certified as both software and a company because data protection and information security are not "extra requirements" for us, but the basis of every collaboration.


%20Large.jpeg)







